Training Courses

Training Courses –
Our Services
Benefit, along with your team, from our in-depth knowledge and many years of experience in IT security through practical training courses.
Application Security Basics
Training for everyone – administrators, software developers, project managers, architects.
OWASP Top 10 – Application Security Quickstart
Best Practices for Secure Web Applications
Application Security in Practice
Training for DevOps & developers
LLM Security Best Practices
DevSecOps: Security in the CI/CD Pipeline
Secure Coding for Mobile Apps
Secure Coding for Java
Penetration Testing
Training for penetration testers
Advanced Application Security Penetration Testing
Basic Training: Performing Penetration Tests
Your trainers
Our promise: from practice, for practice, and always up to date. That's why all our trainers are active experts with many years of experience in their respective fields.
Training format & methodology
Interesting facts about our online training courses
- Live & Interactive
The trainer is live in the studio, allowing you to ask questions and discuss topics via voice and chat at any time. - Hands-On
Our convenient practice environment is available in the cloud. - Individual
No one is left behind. The training is also available as a video stream afterwards. - Full Focus
The use of modern technology ensures a smooth process.
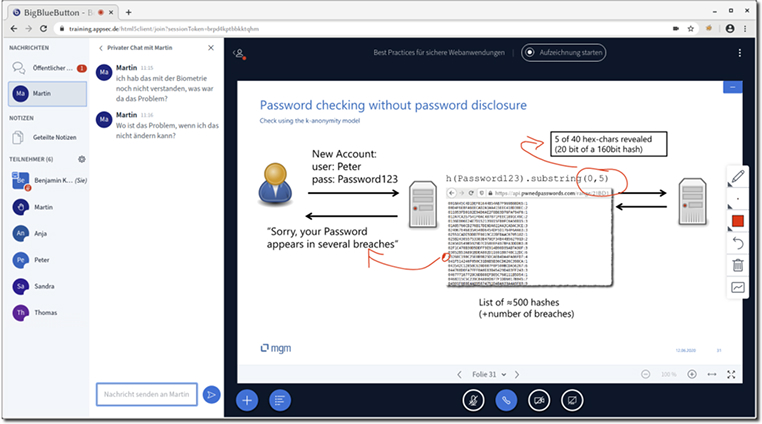
The video conferencing system
We use the BigBlueButton training environment for our online training courses.
The platform is hosted in our data center and dedicated to training, so we don't have to compromise on data protection. A 1 Gbit connection ensures very good performance. Only a modern web browser is required to use the environment; no additional client software needs to be installed.
In addition to classic conference features such as live chat and screen sharing, the training environment also offers support for so-called breakout rooms, which can be used for group exercises, as well as the option for participants to share the slides for editing with a virtual pen.
FAQ
Isn't it very difficult to follow a face-to-face seminar from your home office with concentration?
If the online training is designed as a 1:1 reproduction of a normal face-to-face seminar, that is certainly the case. We have invested a lot of time in preparing the content for online delivery and are convinced that we have largely eliminated the disadvantages and that the advantages are fully realized.
Does real interaction even occur?
Our experience shows that this is the case: the threshold for asking questions is very low in the chat. Prepared, frequently interspersed quizzes therefore provide variety, participants can take control of the medium at any time, and the inclusion of other media such as videos, hands-on exercises, etc. provide further stimulation. We have had these experiences not only in smaller training courses at companies, but also in larger seminars that we have conducted at the TU Dresden.
How can the trainer effectively assist with exercises?
For exercises, we use a training environment that we developed ourselves (https://github.com/mgm-sp/NinjaDVA). Within this environment, the trainer can monitor individual steps within the exercise tasks. This allows the trainer to provide guidance without participants even having to ask questions. Additionally, participants are situationally divided into breakout rooms, which form a separate environment for individual participants or working groups. The trainer can connect at any time and provide individual support.
Doesn't it often happen that people talk over each other due to latency?
This cannot be completely avoided, but measures such as the raise-hands feature of our platform reduce it to the point where it doesn't really present a disruptive factor.
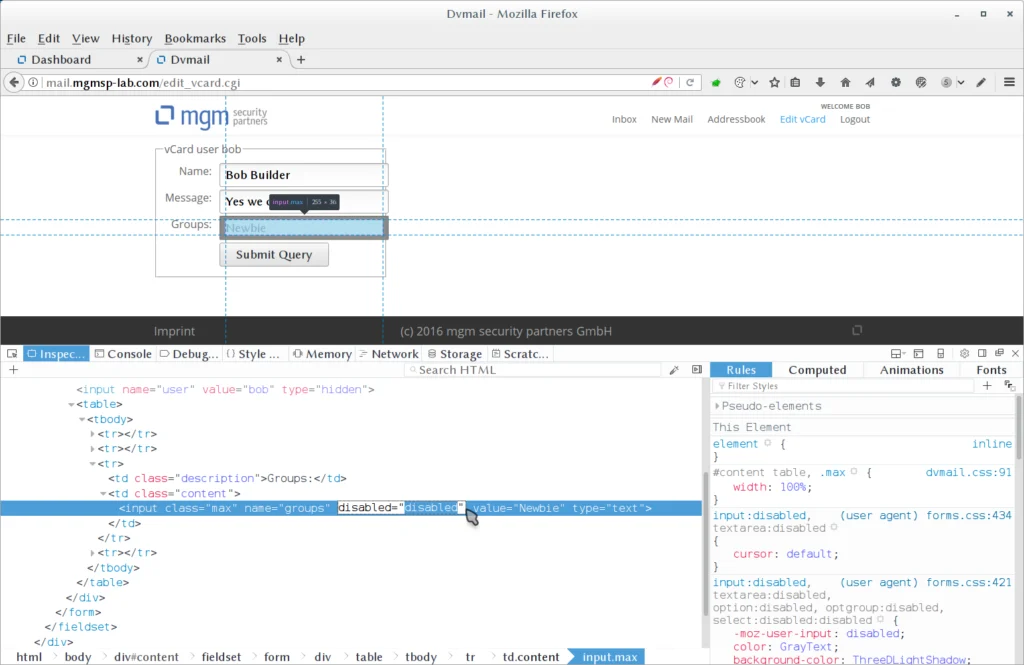
Our training environment NinjaDVA
For our training courses with practical exercises, we use the convenient, mobile training environment NinjaDVA.
This allows participants to directly apply what they have learned and experiment with in-depth exercises.
Particularly important: We adapt to you, not the other way around. That's why we attach great importance to participants using their own laptops with their individual working and development environments.
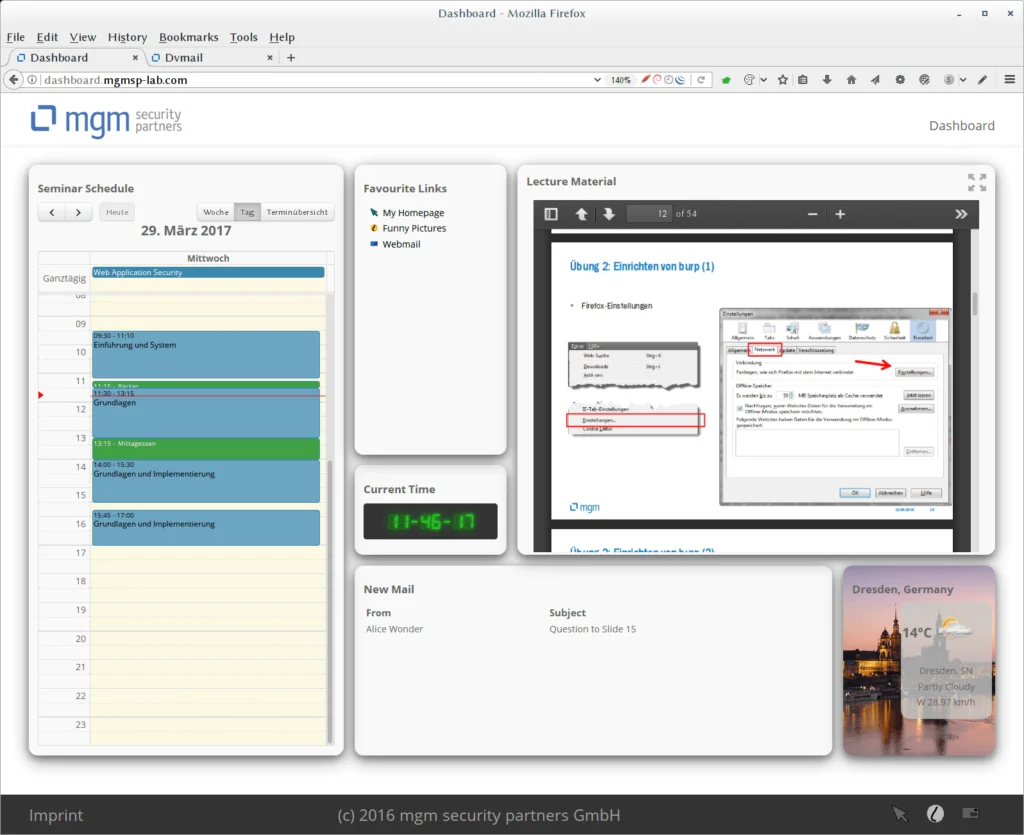
The Dashboard
The Live-Hacking Module
The integration of presentation and training environment also enables participants to experiment effectively and deepen what they have learned with minimal training effort in a highly homogeneous training environment.
The participant has the opportunity to put themselves in the position of an attacker and thus learns to better understand their way of thinking. In an online editor that can be used via the browser, participants can, for example, easily create their own websites to try out various web attacks themselves.
The technical requirements for the clients are minimal. Each participant can use their usual working environment.
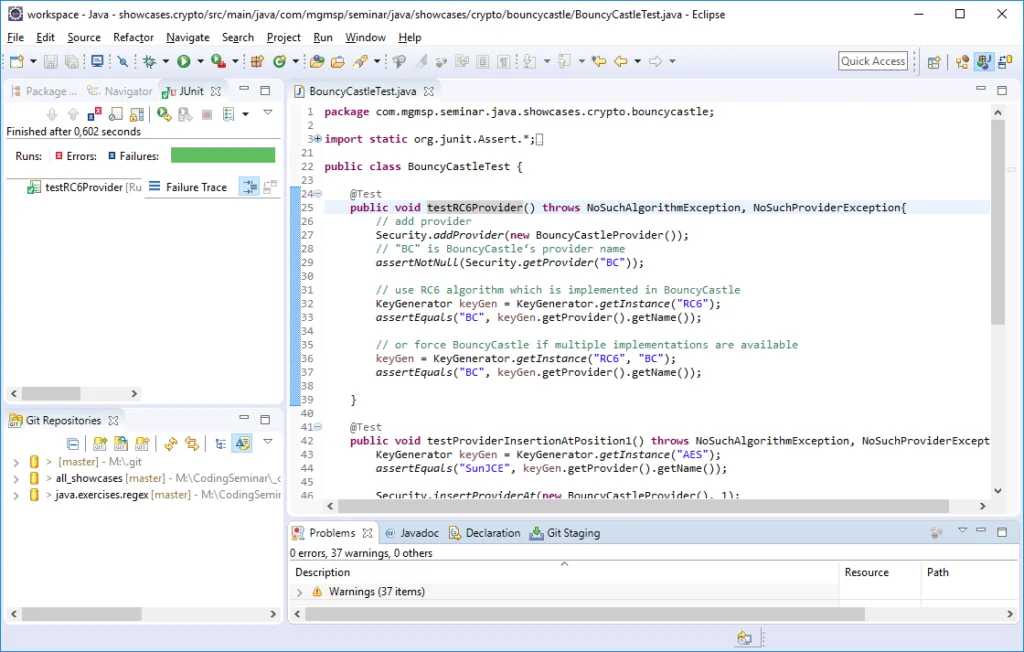
The Secure-Coding Module
After vulnerabilities as well as general and technology-specific countermeasures have been discussed in excerpts in the lecture-accompanying seminar slides, the trainer provides the code (project, modules, classes, etc.) relevant to the current topic in a buildable and executable form in the training environment. Participants can now check out this code into their usual working environment (Eclipse, IntelliJ, etc.) in order to then execute it themselves and experiment with it.
In addition, for many libraries presented in the context of concrete code-specific countermeasures, participants have the opportunity to solve given coding tasks themselves in interactive exercise units. The fulfillment of these exercise tasks is automatically checked after a successful commit to the provided exercise server, and the participant immediately receives corresponding feedback. The trainer can see at any time which participant still needs help and can thus respond quickly and purposefully to individual problems.
Your Benefit
Well-trained employees are the most effective defense against security vulnerabilities. Our training courses equip your team to identify risks and reliably implement standards – practically, up-to-date, and directly applicable.
- From practical experience for practical application: Our trainers are active experts with many years of experience in their respective fields.
- More than 100 companies and over 1,000 trained developers, administrators and security officers.
- Economical for you with as few as 3 to 4 participants.
- Flexible mobile training environment, with content that is always up to date and can be individually adapted to your requirements.
- All training courses can be booked as in-person, online, or hybrid events.