Internet of Things (IoT) Assessment

IoT devices have long been part of our everyday lives and industry – but their networking opens up additional points of entry for attackers.
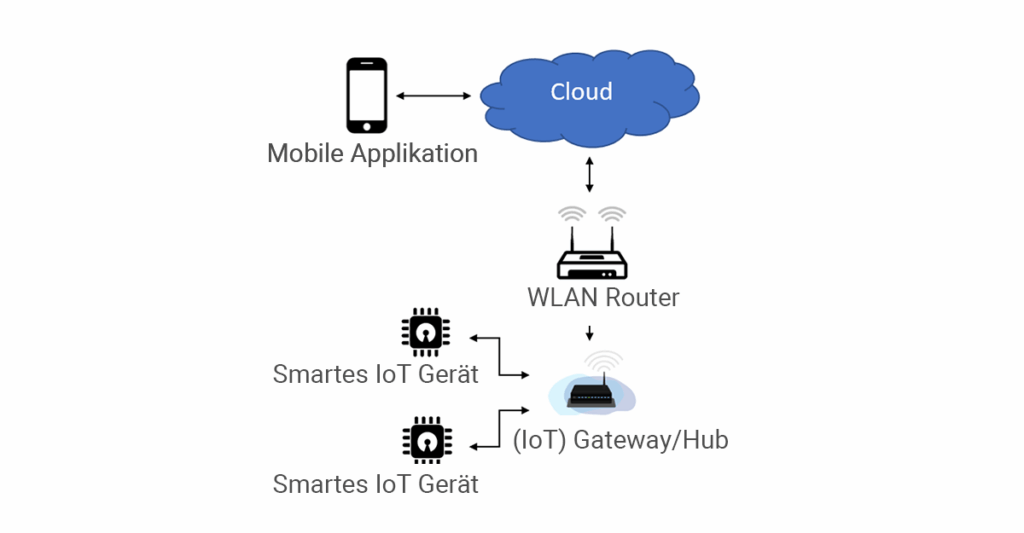
The Internet of Things (IoT) includes smart everyday devices as well as complex machines. They collect data, communicate with each other, and can often be controlled via apps or web interfaces. This variety of components – from hardware to gateways to cloud backends – makes classic penetration tests inadequate. In order to realistically assess the security of IoT environments, an assessment is needed that considers all levels.
Our Services
We offer comprehensive IoT Security Assessments that check all relevant components – hardware, interfaces, network, applications, and cloud backends – for vulnerabilities. The goal is to obtain a complete picture of the security situation of your IoT environment.
In a combined approach, we conduct various types of penetration tests that are specifically tailored to the special features of IoT systems. Each analysis is individually adapted to the target environment. We systematically test all levels – from the physical hardware to the communication protocols to web and mobile applications.
Checkpoints
- Information gathering: Identification of the installed hardware components and interfaces.
- Analysis of common device interfaces (UART, JTAG, SWD, USB).
- Memory chip analysis (reading out firmware and sensitive data).
- Examination of network communication (BLE, ZigBee, WLAN, MQTT, HTTP(S), TCP, …) including service scanning
- Review of the web application according to the standards of the “Web Application Security Pentest”
- Brute-force tests of login services and password cracking of hashes in the graphics card cluster
- Analysis of the mobile app according to the standards of the “Mobile Application Security Pentest”
- Research into known vulnerabilities and misconfigurations, including validation of false positives
- Creation of a detailed results report with concrete recommendations for action in the desired format
Your Benefit
With an IoT Assessment, you gain clarity about the security of your entire IoT infrastructure.
You will receive a holistic assessment that takes into account both classic attack scenarios and IoT-specific risks. This enables you to specifically close vulnerabilities and sustainably secure your systems.
- Coverage of all components: hardware, network, web and mobile
- Individually tailored test procedures
- Combination of proven penetration tests and IoT-specific methods
- Validated results without false positives
- Detailed results report with practical measures