Application Security Penetration Tests

Penetration tests are the most straightforward way to assess the security of applications and systems. We have been offering this service for over 20 years, leveraging the experience gained from thousands of tested applications for hundreds of companies.
A penetration test simulates the perspective of a real attacker and verifies whether and how identified vulnerabilities can actually be exploited in practice. This reveals technical security gaps as well as faulty configurations or unrecognized interactions between components – often precisely where purely static analyses reach their limits.
Our Services
We examine your applications for vulnerabilities and anomalies using penetration tests. Our approach is based on current standards. In doing so, we incorporate your individual threat scenarios and industry-specific risks. Our reports provide decision-makers with a basis for decision-making and developers with concrete instructions for action.
The Grey Box Penetration Test is the approach with the best price-performance ratio and in most cases the method of choice.
In the Grey Box Penetration Test, the tester receives a maximum of information about the application, its internal structure and the technology stack used. For all application functions, roles and rights, appropriate users are made available to the tester.
The Grey Box approach enables maximum efficiency in the use of the provided time budget.
In the White Box Penetration Test, the tester also gains insight into the application's source code.
The availability of the source code enables:
- More targeted review of suspected vulnerabilities
- Detection of potential gaps that cannot be reliably detected with a penetration test or only with great effort
- Overall, a greater coverage
Comprehensive Static Code Analysis (SAST) goes even further than a Greybox Penetration Test. We offer code analysis as a supplement to penetration testing or separately..
The Blackbox Penetration Test is used for specific tasks.
In a Black Box Penetration Test, the tester receives no additional information, and is therefore in the same situation as a third party. This is about answering the question “What can an attacker achieve without possessing additional information or rights?”.
This approach only offers a limited statement regarding the task to be strived for in the field of application security: “Find all vulnerabilities and security problems” and is therefore only suitable in special cases.
How we test
Our investigations are based on existing standards and best practices, as well as over 25 years of experience.
In the past, we have contributed to the development of several application security standards. We are still active in the Open Web Application Security Project (OWASP) and contribute our expertise.
- OWASP ASVS (Application Security Verification Standard)
- OWASP Testing Guide
- OWASP Top 10
- OWASP Development Guide
- Web Application Security Consortium (WASC) Threat Classification
- PCI Data Security Standard (PCI-DSS)
- BSI guidelines “Implementation Concept for Penetration Tests” and “Catalog of Measures and Best Practices for Web Application Security”
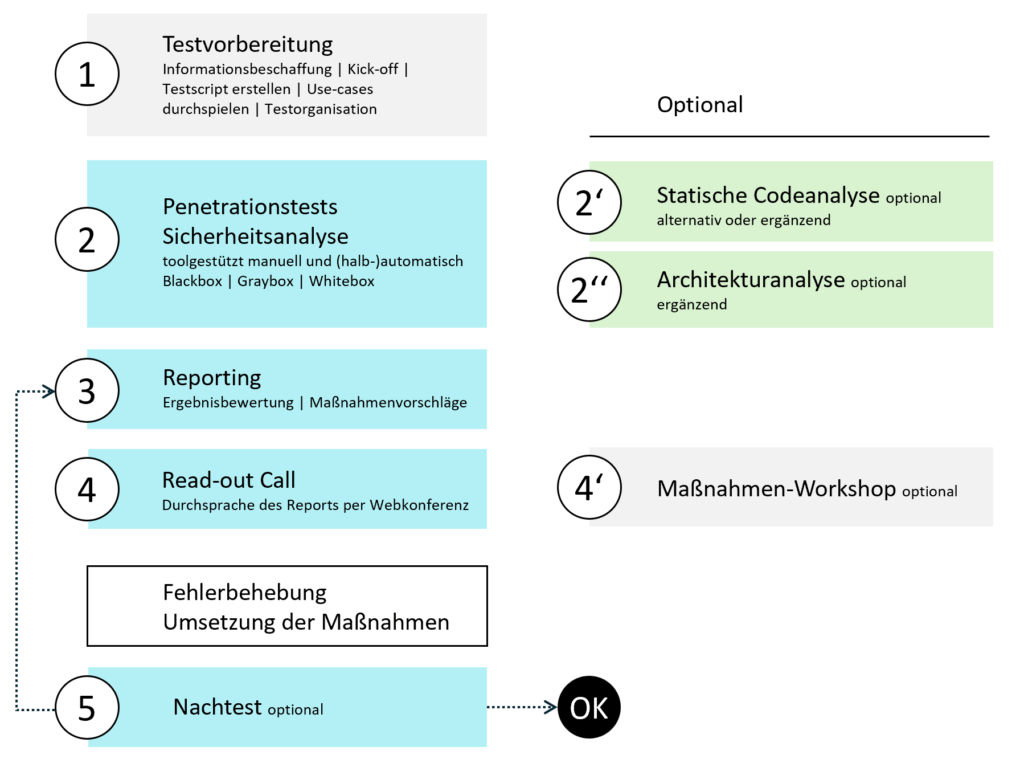
Our standardized process ensures efficiency while maintaining flexibility in the face of unexpected obstacles on the client's side.
Results report
As a result, you will receive a comprehensive report that presents the test cases and identified issues in an easily comprehensible manner, providing information about the potential hazards and threats. Furthermore, we provide detailed instructions on how to rectify them.
In the final report, we not only list the findings – the discovered vulnerabilities – but also specify the test results for each vulnerability category. This ensures transparency regarding whether an unlisted vulnerability category was tested but yielded no findings, or whether the corresponding test was not conducted at all.
Assessment of hazard potentials
- [low] – The vulnerability is classified as low. Addressing this issue in the long term should be considered.
- [medium] – The vulnerability is classified as medium and should be resolved in a timely manner.
- [high] – The vulnerability is classified as high. An assessment of the actual risk and a decision on measures must be taken immediately.
- [critical] – The vulnerability is classified as critical. Immediate action must be taken.
- [OK] – The application was examined for the specified vulnerability, but it was not found.
- [Info] – A potentially helpful piece of information about a detected anomaly, but not a vulnerability.
Note: The hazard potential is an intuitively understandable measure of the severity of the vulnerability. It is not to be confused with the real risk that a finding represents. To assess the risk (= damage amount * probability of occurrence), further information is generally required, in particular the amount of the maximum damage occurring in the event of exploitation. The risk assessment is then relevant if the remediation is associated with comparatively high direct or indirect costs.
- [Info] – For information only, not a vulnerability.
- [low] – The vulnerability is classified as low. Addressing this issue in the long term should be considered.
- [medium] – The vulnerability is classified as medium and should be resolved in the medium term.
- [high] – The vulnerability is classified as high and should be resolved in the short term.
- [critical] – The vulnerability is classified as critical. Immediate action should be taken.
- [OK] – The application was examined for the specified vulnerability, but it was not found.
Assessment of the probability of occurrence
.
- [Info] – For information only, not a vulnerability.
- [low] – The vulnerability is classified as low. Addressing this issue in the long term should be considered.
- [medium] – The vulnerability is classified as medium and should be resolved in the medium term.
- [high] – The vulnerability is classified as high and should be resolved in the short term.
- [critical] – The vulnerability is classified as critical. Immediate action should be taken.
- [OK] – The application was examined for the specified vulnerability, but it was not found.
Structure of the test results
There is a separate sub-chapter for each vulnerability or attack technique. The following are listed in each case:
- Explanation: The vulnerability or attack technique is explained in a generally understandable way and references to further sources of information are provided (e.g. links).
- Attack Scenario / Threat: If necessary, we describe possible scenarios for exploiting the vulnerability found in order to give the reader the opportunity to assess the risk. We base this on a worst-case approach, i.e. in case of doubt, we describe the more threatening scenario. This description is independent of the probability of occurrence.
- Test Cases and Examples: The tests carried out are described in detail and documented with screenshots, so that it is easy for the client to understand them and assess the potential danger themselves.
- Measure: Wherever possible, we provide general measures and best practices for solving the problem found.
Your Benefit
Our Application Security Penetration Tests specifically uncover vulnerabilities in web and mobile applications before attackers can exploit them. They help to assess security risks and implement effective countermeasures to sustainably protect data, systems and business processes.
- Comprehensive – The investigation covers all standards of the Open Web Application Security Project (OWASP).
- Reliable – The wealth of experience stored in our knowledge pool and the high level of expertise of our testers ensure maximum reliability in the search for vulnerabilities.
- Efficient – Thanks to our experience and the use of powerful tools, we achieve a high level of efficiency – and can therefore offer correspondingly favorable prices.