DORA – IT security tests for digital resilience

DORA places high demands on the digital resilience of companies – we help you implement your testing requirements in a risk-based, efficient and simple manner.
What is DORA?
DORA (Digital Operational Resilience Act) is an EU regulation designed to ensure that financial companies throughout the European Union become more resilient to IT risks. The focus is on ensuring digital operational stability and the ability to detect, defend against and manage IT disruptions. A central component is comprehensive testing procedures, which also include IT security tests or penetration tests (pentests) to uncover security vulnerabilities.
Who does DORA affect?
The regulation applies to financial companies such as banks, insurance companies, payment service providers and securities traders, as well as IT service providers that provide critical services for these organizations. Smaller financial service providers and their suppliers are also affected by the requirements.
Why is DORA useful?
In an increasingly networked and digitized world, financial companies are more than ever the target of cyber attacks. DORA helps to close IT security gaps, meet regulatory requirements and avoid financial losses due to IT failures or cyber incidents. In particular, pentests are an effective means of identifying and fixing vulnerabilities before they can be exploited by attackers. The regulation provides companies with a clear framework to strategically improve their IT security and strengthen digital resilience in the long term. In doing so, DORA creates trust among customers, partners and supervisory authorities.
IT security tests within the framework of DORA
The DORA regulation requires companies to conduct regular IT security tests to identify and fix vulnerabilities – including the more specialized Threat-Led Penetration Tests (TLPT), which are particularly important for critical institutions.
Security Analyses
Objective: Security analyses, e.g. in the form of penetration tests, are a fundamental instrument for complying with the requirements of the DORA regulation regarding the security of IT systems. They serve to identify vulnerabilities in the IT landscape at an early stage, before they can be exploited by real attackers. With the help of practical attack simulations, the security of networks, applications and processes is checked in order to minimize risks and increase resilience against cyber threats.
Additional requirements
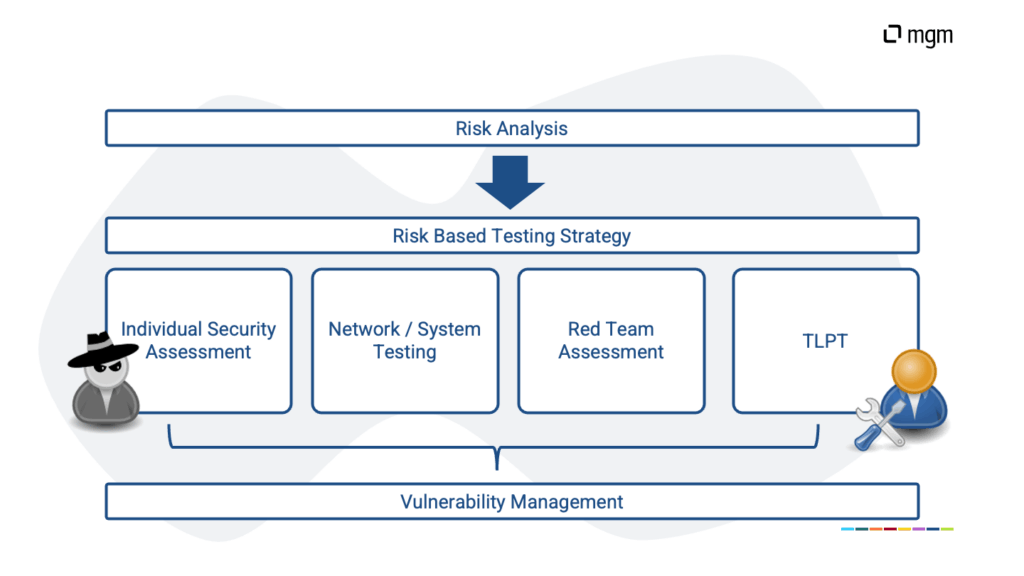
- Risk-based approach: Tests must be planned and carried out on the basis of a risk analysis.
- Realistic attack scenarios: Tests should simulate practical attacks to identify vulnerabilities under real-world conditions.
- Independent execution: Tests must be performed by qualified, independent experts or external service providers.
- Regularity: Tests must be carried out at regular intervals and at least once a year.
- Comprehensive reporting: Test results must be documented, analyzed, and reported to relevant stakeholders.
- Follow-up measures: Identified vulnerabilities must be prioritized and resolved promptly to minimize risks.
Threat Led Penetration Testing (TLPT)
Objective: Threat-Led Penetration Testing (TLPT) is an advanced requirement of the DORA regulation introduced for systemically important financial institutions. Building on the TIBER-EU framework, TLPT aims to assess the resilience of IT systems and business processes against sophisticated cyberattacks. Through realistic, threat-driven simulations, vulnerabilities are identified and remediated to sustainably strengthen operational resilience.
Additional requirements:
- Advanced risk analysis: TLPT is based on a detailed, risk-based threat analysis that specifically incorporates current attacker profiles and realistic attack methods.
- Threat-driven simulations: The tests reflect sophisticated, targeted cyberattacks tailored to the company's individual vulnerabilities and business processes.
- Integration of Red Teaming techniques: TLPT utilizes comprehensive Red Teaming approaches to test IT infrastructure, processes, and personnel under real-world conditions.
- Mandatory for selected financial institutions: TLPT is mandatory exclusively for financial institutions classified as critical infrastructure by supervisory authorities and notified to perform it.
- Regularity: TLPT must be performed at least every three years or when significant changes occur in the IT and business landscape.
- Evaluation of results by supervisory authorities: The test results must be documented, analyzed, and submitted to the competent supervisory authorities.
Your expert for tailored solutions
With our many years of experience, we are ideally equipped to support you in implementing your testing requirements.
- Risk assessment: We support you in developing a risk-based testing program, conduct a threat analysis of your IT landscape, and recommend a solution that is precisely tailored to your requirements.
- Initial determination of the security level using a Red Teaming Assessment: A Red Teaming Assessment provides you with a realistic, holistic view of your organization's actual resilience against targeted attacks. Through simulation-based tests, we identify security gaps that often remain hidden in classic analyses – across technical, organizational, and human vulnerabilities. The results form a well-founded basis for your further security strategy.
- Creation of a customized testing strategy: Based on your individual risk situation, we work with you to develop a targeted testing strategy. We define suitable testing methods, prioritize critical systems, and create a structured basis for continuous security analyses.
- Vulnerability Management: We support you in establishing a structured process for classifying and prioritizing vulnerabilities in your IT landscape, whether resulting from external penetration tests or internal scans. We help you derive and validate the right measures to maintain a holistic overview.
- Range of testing services:
- Penetration tests: Our investigation covers all 5 levels in the classification scheme for the organization of security in web applications of the German Federal Office for Information Security (BSI) and follows the recommendations of the Open Worldwide Application Security Project (OWASP).
- Source code analyses: We uncover security problems directly in the source code and guide the developers to the root of the problem.
- Infrastructure investigations: As a basis for secure applications, the system and the network infrastructure should not be neglected. We examine both for vulnerabilities.
- and much more!
- TLPT Support: We assist you in preparing for and conducting a Threat-Led Penetration Test (TLPT) in accordance with DORA requirements. From coordination with the supervisory authority and threat modeling to execution and reporting, we ensure professional implementation that meets regulatory requirements and delivers genuine added value for your security strategy.
Comprehensive support for DORA
DORA places extensive demands on financial institutions, from risk management and supply chain security to operational resilience. Do you have questions about implementing DORA in your IT beyond security testing? We are happy to support you with comprehensive advice on all aspects of information security. More information can be found here.
