Secure digital growth - IT security as an enabler of digital transformation

Why is this topic important?
Digitalization offers numerous opportunities for companies, but also new risks. Cyberattacks are steadily increasing, and at the same time, regulatory requirements are rising, for example through NIS2 or DORA. Those who do not act in good time risk not only financial and legal consequences, but also the loss of trust and market share.
IT security doesn't have to be complicated. Simple, practical security concepts can effectively minimize risks without creating unnecessary complexity.
We help companies design their security strategy to meet regulatory requirements and drive digitization safely and successfully.
Our core thesis: IT security is not an obstacle, but an enabler of digitalization.
Companies that see IT security not as an obstacle, but as a strategic success factor, benefit in several ways. Targeted integration creates efficiency, resilience and trust.
- Efficiency: Secure automation and digital workflows optimize processes and reduce costs in the long term.
- Resilience: A well-thought-out security concept protects against data loss, reputational damage and regulatory sanctions.
- Trust: Customers and partners are increasingly relying on trustworthy companies with high security standards.
The simple and early integration of security reduces long-term efforts and ensures sustainable stability - without unnecessary complexity.
Strategy & Governance
Sustainable IT security begins with a clear strategy. This is not just about technical measures, but also about closely linking business and security goals.
- Business & Security Alignment: IT security must not be an isolated topic. It must be seamlessly integrated into the corporate strategy and support business processes instead of hindering them.
- Compliance as a competitive advantage: Regulatory requirements such as NIS2 or DORA are not just mandatory; they can also serve as a quality seal. Companies that actively shape their security strategy gain the trust of customers and partners.
- Individual security strategies: Every company faces different challenges. We develop tailored security concepts and help you set up an information management system to minimize risks, optimize processes, and securely shape your digital transformation.
TODO-Link: Learn more about our consulting services in information security here.
Technology & Architecture
A strong IT security strategy starts with the right technological foundation. Modern companies rely on agile architectures in which security and the trustworthy handling of data are considered from the outset.
- Security and Privacy by Design: Security and data protection must be integrated directly into development and process modeling – not as a subsequent measure, but as an integral component of every architecture.
- Cloud, DevSecOps & AI: The secure use of cloud technologies, the automation of security processes in DevSecOps pipelines for software development, and the responsible use of Artificial Intelligence are central challenges for modern IT architectures.
- mgm Atlas (TODO:Link to ATLAS): With our Application Security Posture Management (ASPM) tool, companies always maintain an overview of their security situation, enabling them to detect threats before they become security incidents.
- Technical security analyses: Through targeted reviews such as penetration tests, code reviews, and red teaming, we identify vulnerabilities early on and help you proactively eliminate security risks.
Culture & Awareness
Technology alone is not enough to protect companies sustainably. A strong security culture and the awareness of all employees are crucial success factors.
- CISO as Business Partner: Information security must not be a purely IT matter. A well-positioned CISO supports not only IT but also management in integrating security strategies into business decisions.
- Training & Awareness for all: From developers to specialist departments – IT security affects everyone in the company. Practical training and interactive formats help to identify risks and act in a security-conscious manner.
- Holistic awareness concepts: Security awareness must be established at all levels – from employees to executives. We develop tailored awareness programs that make security a matter of course.
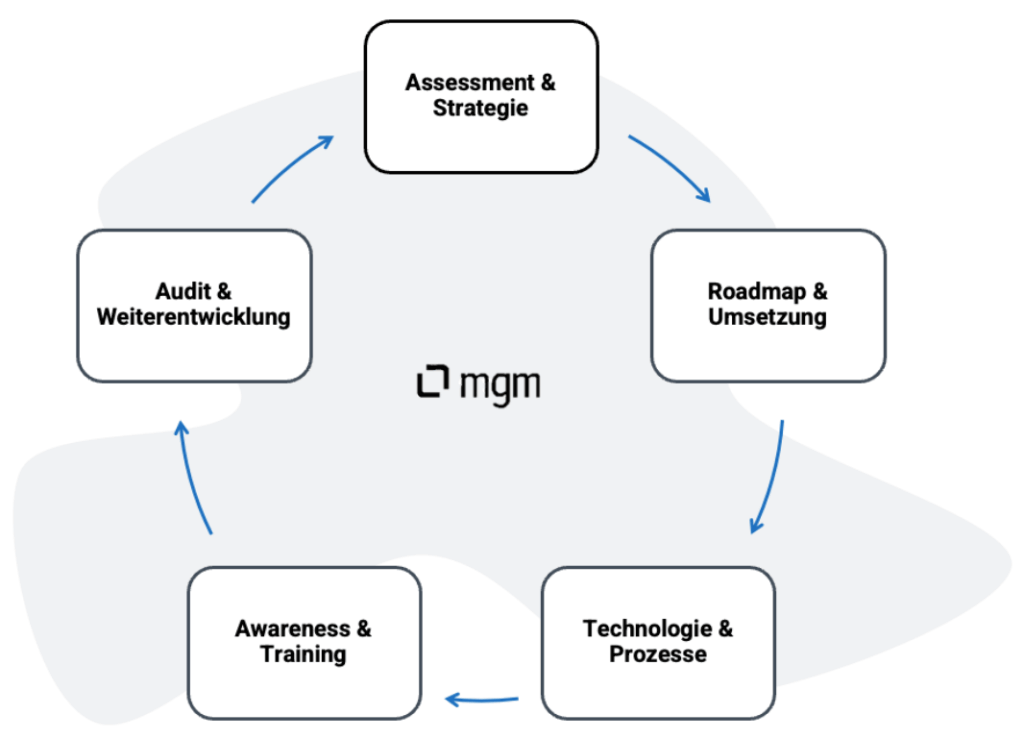
Our Approach - The Secure Transformation Path
A successful digital transformation requires a well-thought-out and secure approach. We support companies on their path to greater IT security – individually, pragmatically, and without unnecessary complexity. Our transformation path ensures sustainable security that integrates seamlessly into business processes.
- Assessment & Strategy – Where does your company stand? What risks exist? We analyze your current security situation and develop tailored strategies. (Individual analysis)
- Roadmap & Implementation – A secure transformation plan must be realistic and efficient. We develop a lean and pragmatic security roadmap that can be implemented without disrupting operations. (Lean & pragmatic)
- Technology & Processes – Cloud security, DevSecOps, AI, and automation are essential components of modern IT architectures. We help you technically secure your solutions. (Practical & understandable)
- Awareness & Training – IT security starts with people. We train teams to minimize security risks early on. (Practical & understandable)
- Audit & Continuous Improvement – Regular tests, security reviews, and the optimization of your security governance ensure that your company remains permanently protected – without unnecessary bureaucracy. (Efficient & sustainable)
Why mgm security partners?
In a world full of cyber threats, more than standard solutions are needed. We offer tailored IT security strategies that not only look good on paper but also prove themselves in practice.
- 25 Years of IT Security Expertise – Benefit from our in-depth specialist knowledge and many years of experience in technology and organization.
- Practical, Implementable Solutions – We focus on security that works. No unnecessary effort, no superfluous bureaucracy – but pragmatic solutions that integrate seamlessly into your business processes.
- Individual Consulting – Every company is unique. We develop tailored security strategies that fit your organization – efficient, economical and effective.
- End-to-End Support – From the initial analysis, through penetration tests and training, to implementation, we support you in every phase of your security strategy.
- Long-Term Partnerships – Security is not a one-off project, but an ongoing process. We are at your side as a reliable partner and support you with sustainable security concepts.
“We simplify your Information Security Journey” – Information security made easy.
Your Benefit
Companies that see IT security not as an obstacle, but as a strategic success factor, benefit in several ways. Targeted integration creates efficiency, resilience and trust.
The simple and early integration of security reduces long-term efforts and ensures sustainable stability - without unnecessary complexity.
- Efficiency: Secure automation and digital workflows optimize processes and reduce costs in the long term.
- Resilience: A well-thought-out security concept protects against data loss, reputational damage and regulatory sanctions.
- Trust: Customers and partners are increasingly relying on trustworthy companies with high security standards.