Mobile App Security Testing
Mobile apps have become an indispensable part of everyday life – making it all the more important to consistently check their security. Our Mobile App Security Testing reliably uncovers vulnerabilities in the app, communication, and backend systems.
Whether in banking, e-commerce, or healthcare, mobile applications process highly sensitive data and must meet the highest security standards. The common misconception that apps are self-contained systems is misleading. Attackers can analyze and manipulate not only the app’s internal workings but also its communications and server-side interfaces.
This significantly increases the complexity of securing these systems—and with it, the need for comprehensive security analyses that go beyond traditional web application testing.
Our Services
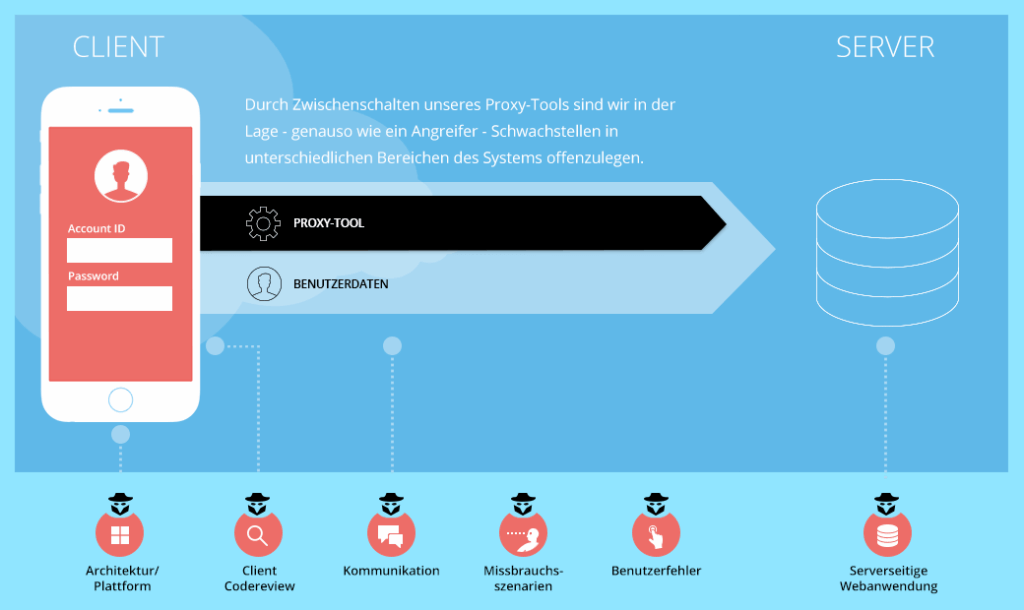
We analyze your mobile app holistically – from the client to the communication to the backend. Depending on the app type, platform, and protection requirements, we use different test methods.
- Server-side web application: Performing penetration tests on the backend systems.
- Communication: Decryption and analysis of data transmission between app and server.
- Architecture: Platform-specific analysis of the app architecture to ensure compliance with security guidelines and security-related platform features.
- Code analysis: Selective or comprehensive examination of the source code for security-critical points, especially when processing and storing sensitive data.
- Abuse scenarios & user errors: Assessment of typical risks such as device loss, theft, or incorrect usage.
- OWASP Mobile Testing Guide: Coverage of all common vulnerabilities according to the current standard.
Approach
Our approach is based on proven standards and is individually tailored to your app.
The goal is a practical security assessment that considers realistic attack paths.
- Kick-off & Scoping: Coordination of objective, scope, and testing methodology.
- Blackbox Tests: Penetration tests against the app and backend without prior knowledge to simulate realistic attacks.
- Detailed Analyses: Architecture and code reviews depending on the protection requirements.
- Attack Simulations: Testing of typical abuse and error scenarios.
- Evaluation & Reporting: Detailed report with risk assessment and recommended actions.