HTML Injection Vulnerability in Vaultwarden Admin Dashboard
Do you trust the secure management of your access data? Admin dashboards are the focus of many attacks because they offer central access to important user and organization data. On behalf of the German Federal Office for Information Security (BSI), we specifically examined Vaultwarden using static code analysis and penetration tests. In the process, we discovered a critical HTML injection security vulnerability in the admin dashboard up to and including version 1.30.3.
Attackers were able to inject specially crafted HTML content into the “Organization” and “User” fields. These were incorrectly displayed in the admin dashboard and could potentially be used to redirect administrators to manipulated websites or falsify the appearance of the dashboard. Although Vaultwarden's strict Content Security Policy effectively prevents JavaScript attacks, exploitation possibilities remain, such as unwanted redirects.
We reported the vulnerability immediately, and the developers provided a solution in version 1.32.0.
In this article, you will learn how the security vulnerability came about, what risks exist for your company, and how you can effectively protect yourself. Take advantage of our independent expertise. We would be happy to advise you on all aspects of your IT security and support you in keeping your systems up to date.
An HTML injection vulnerability was discovered in Vaultwarden version 1.30.3 (or earlier). We reported this vulnerability to the developer, who fixed the problem and closed the vulnerability in version 1.32.0.
Description
Vaultwarden ships with an admin dashboard. This feature can be enabled according to the instructions described here: https://github.com/dani-garcia/vaultwarden/wiki/Enabling-admin-page
Once enabled, the Vaultwarden admin dashboard is available under /admin. The Vaultwarden admin dashboard has a page for user management. For users who are members of an organization, the administrator can quickly change the role assignment via a modal dialog.
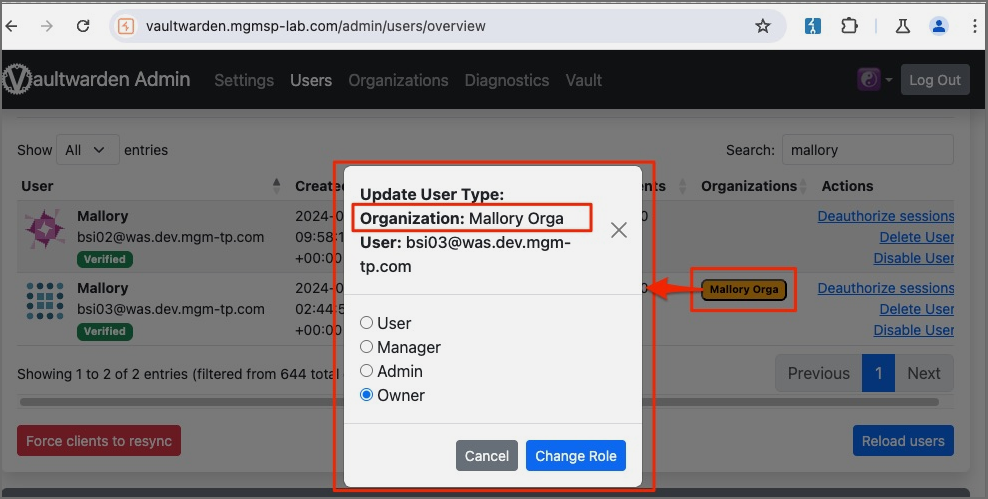
This modal dialog is vulnerable to HTML injections. Payloads can be injected into the "Organization" and "User" fields. To demonstrate the issue, the following payload was stored in the "Organization" field.
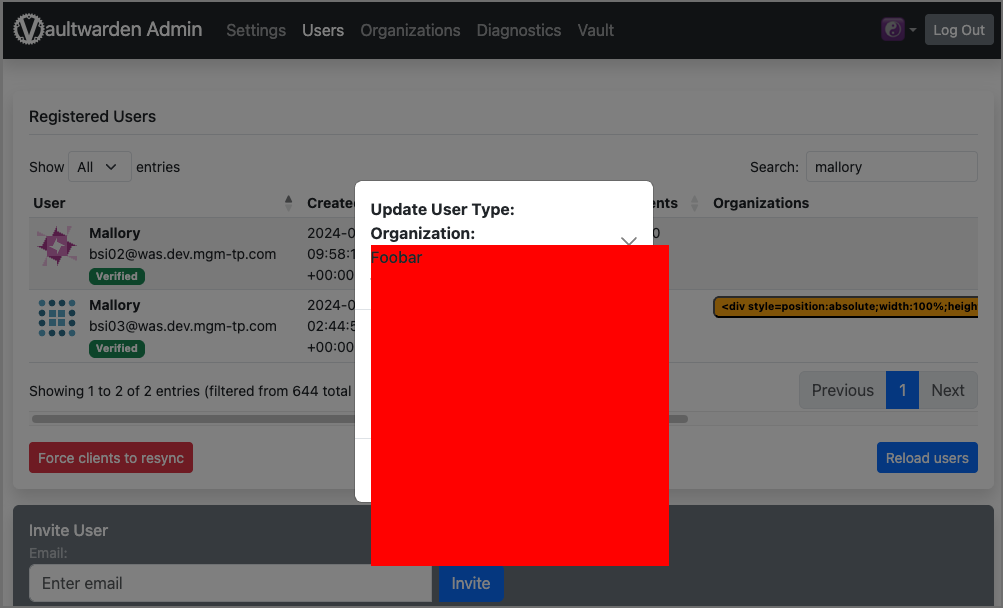
<div style=position:absolute;width:100%;height:100%;background:red;z-index:9>Foobar</div>
The injected payload was parsed as HTML code and rendered on the vulnerable page:
Note that Vaultwarden uses a very strict Content Security Policy (CSP) by default. This CSP successfully prevents attempts to execute JavaScript via the injected HTML code.
content-security-policy:
default-src ‚self‘;
base-uri ‚self‘;
form-action ‚self‘;
object-src ‚self‘ blob:;
script-src ‚self‘ 'wasm-unsafe-eval';
style-src ‚self‘ 'unsafe-inline';
child-src ‚self‘ https://*.duosecurity.com https://*.duofederal.com;
frame-src ‚self‘ https://*.duosecurity.com https://*.duofederal.com;
frame-ancestors ‚self‘ chrome-extension://nngceckbapebfimnlniiiahkandclblb chrome-extension://jbkfoedolllekgbhcbcoahefnbanhhlh moz-extension://* ;
img-src ‚self‘ data: https://haveibeenpwned.com ;
connect-src ‚self‘ https://api.pwnedpasswords.com https://api.2fa.directory https://app.simplelogin.io/api/ https://app.addy.io/api/ https://api.fastmail.com/ https://api.forwardemail.net ;However, some exploitability is still possible. For example, the following payload could be used to redirect affected users to arbitrary other pages when calling the dialog.
<meta name=language content=1;https://www.mgm-sp.com HTTP-EQUIV=refresh />
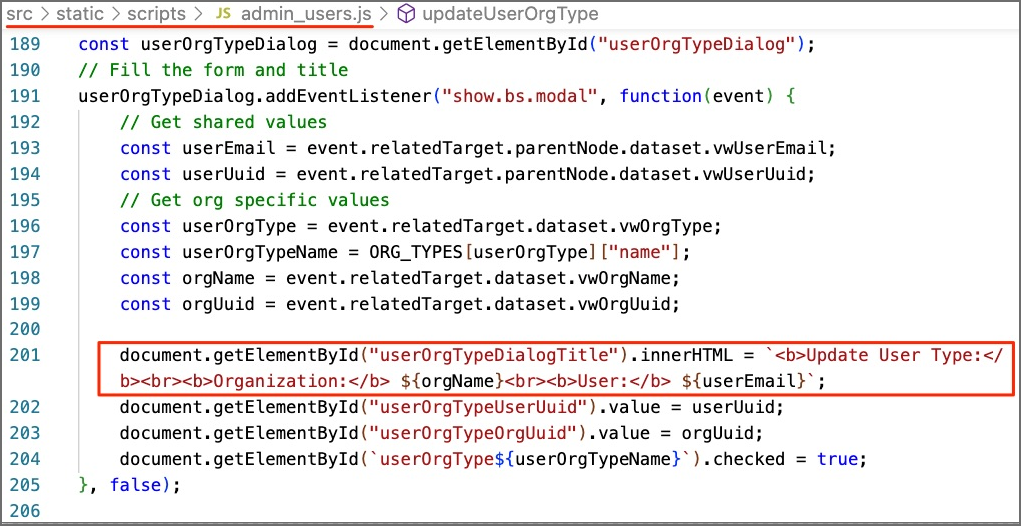
The vulnerable source code can be found here: https://github.com/dani-garcia/vaultwarden/blob/1.30.3/src/static/scripts/admin_users.js#L201
Assigned CVE: https://nvd.nist.gov/vuln/detail/CVE-2024-39926
Affected component: https://github.com/dani-garcia/vaultwarden/
Attack type: Remote
Impact Code Execution: Yes
Attack vectors: To exploit the vulnerability, the user must click on a malicious link prepared by the attacker.
Reference:
https://github.com/dani-garcia/vaultwarden/pull/4737
https://github.com/dani-garcia/vaultwarden/releases/tag/1.32.0

