Vaultwarden Security Vulnerability in Emergency Access
In today's digital landscape, safeguarding sensitive access credentials is of paramount importance, especially concerning emergency functions in password managers like Vaultwarden. As part of a project for the German Federal Office for Information Security (BSI), we conducted a comprehensive security assessment of Vaultwarden and other open-source solutions, identifying a critical vulnerability in the emergency access feature.
The security vulnerability affected Vaultwarden up to and including version 1.30.3, allowing beneficiaries to independently adjust the access conditions after initiating emergency access. This made it possible to obtain higher access rights or bypass the prescribed waiting period, contrary to the grantor's specifications. In a critical situation, this could have led to an unintended complete account takeover.
We reported this vulnerability, and the developers promptly addressed the issue, implementing the necessary protection with version 1.32.0.
In this article, you will learn how the vulnerability arose and why regular reviews of even well-established security solutions are so important. Would you like to know if your systems are affected and how you can optimally protect yourself? Take advantage of our expertise – we are happy to support you with all questions regarding your IT security.
In Vaultwarden version 1.30.3 (or earlier), a missing authentication check was identified, which allowed modification of the metadata of an emergency access. We reported this vulnerability to the developer, who fixed the issue and patched the vulnerability in version 1.32.0.
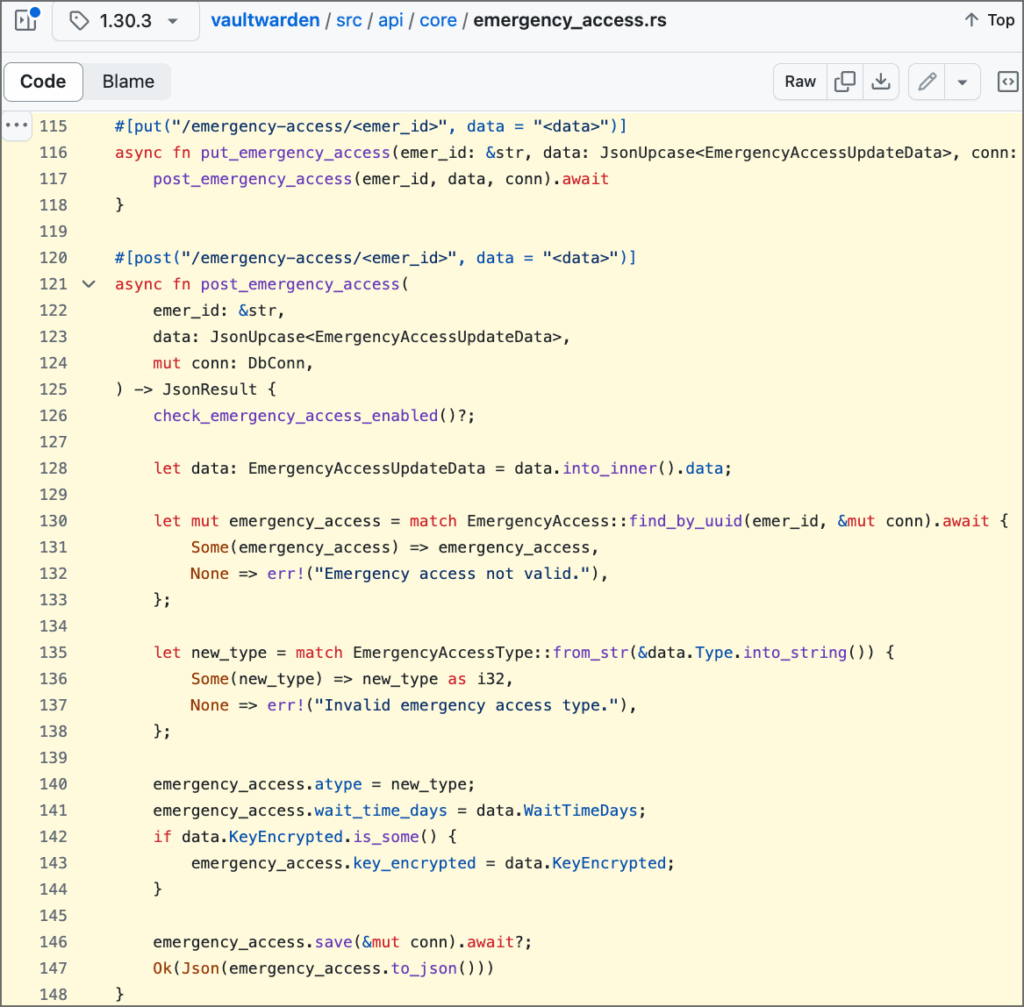
Once emergency access was initiated, the beneficiary could modify the access conditions, including the access level and the waiting period. This allows the beneficiary to access the grantor's data with a higher access level (full account takeover instead of read-only access) and without the set waiting period expiring (7 days by default). This renders the access restriction set by the grantor ineffective. This access control vulnerability only affects the API endpoint for modifying emergency access. At the endpoint for creating the emergency access, Vaultwarden correctly checks the user permissions. The exploitability of this finding is therefore limited to the designated beneficiary gaining higher permissions to access the grantor's data. No vulnerabilities were found that would allow the unauthorized creation of emergency access for a specific user.
Description
Emergency access is a feature of Vaultwarden that allows a user (grantor) to designate a trusted contact (beneficiary) who can request access to their vault data in an emergency.
When setting up emergency access, the grantor can define several conditions for the granted access, including
- Access level: Determines whether the beneficiary has read-only access to the grantor's data or whether the beneficiary is allowed to take over the grantor's account.
- Waiting period: Determines how long the beneficiary must wait after initiating emergency access to access the grantor's data. This waiting period gives the grantor a window of time in which to revoke emergency access.
For more information about Vaultwarden's emergency access, please visit the emergency access page of the upstream Bitwarden server.
Sobald der Notfallzugriff initiiert wurde, können seine Metadaten über den API-Endpunkt PUT /api/emergency-access/<access_UUID> geändert werden. Auf diese Weise kann der Berechtigunggeber die von ihm erstellten Notfallzugriffsbedingungen ändern, einschließlich der Zugriffsebene und der Wartezeit.
It was found that Vaultwarden does not perform access control at this API endpoint. Our tests have shown that even an unauthenticated user can modify the emergency access with arbitrary data if the access UUID is known. The following screenshot illustrates the problem.
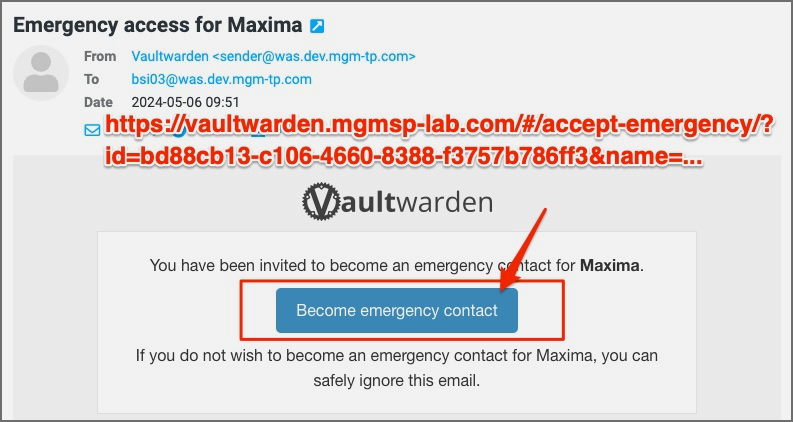
To modify an emergency access, the valid access UUID must be specified as a request parameter. Vaultwarden uses UUID version 4 for entity IDs, which are difficult to enumerate. Nevertheless, the beneficiary was able to find this information in the notification email:
The affected source code can be found here: https://github.com/dani-garcia/vaultwarden/blob/1.30.3/src/api/core/emergency_access.rs#L115-L148
Assigned CVE: https://nvd.nist.gov/vuln/detail/CVE-2024-39924
Affected component: https://github.com/dani-garcia/vaultwarden/
Attack type: Remote
Attack vectors: To exploit the vulnerability, a malicious user must be granted "low" emergency access to another user's vault.
Reference:
https://github.com/dani-garcia/vaultwarden/pull/4715
https://github.com/dani-garcia/vaultwarden/releases/tag/1.32.0

