“Drone Harmony for DJI Dock” is an application developed by Drone Harmony AG that allows users to define flight routes for drone inspections, view the drone's live stream, and control the drone in real time.
To ensure the security of using this software solution, mgm security partners was commissioned by its client Vattenfall in December 2024 to perform a penetration test.
As a result of this comprehensive penetration test, several vulnerabilities were identified by mgm security partners and fixed by Drone Harmony.
Summary
Several security-relevant vulnerabilities were identified in the application, potentially leading to unauthorized privilege escalation. For example, authenticated users were able to delete saved locations of other users. Furthermore, users with read-only access could illegitimately upload media and overlays, as well as remove existing content.
Additionally, it was found that arbitrary files could be uploaded and downloaded via the web application. This vulnerability enabled reflected Cross-Site Scripting (XSS) attacks, where malicious HTML files with XSS payloads could be uploaded and distributed to other users via corresponding download links.
Further security risks concerned the transmission of session tokens in URL parameters and the disclosure of the password for MQTT access to drone communication in the user interface. The former poses the risk of unauthorized account access via logged or cached URLs, while the latter can – for example, in combination with an XSS attack – lead to the takeover of MQTT communication.
All identified vulnerabilities were reported to the manufacturer as part of a responsible disclosure process and were fixed with the software releases of April 23 and May 20, 2025. Further details are published under the following link: https://www.droneharmony.com/post/security
CVEs have been requested for the vulnerabilities.
Further details on the vulnerabilities are described in the following sections:
Privilege Escalation
Description
The application is vulnerable to horizontal and vertical privilege escalation in two functionalities:
File Upload (vertical privilege escalation)
The application allows users to add other users to their team and grant them restricted access rights. However, the rights verification only takes place in the frontend. This allows a user to bypass this check. For example, a user with read-only rights could upload or delete media.
Example of a call to upload media:
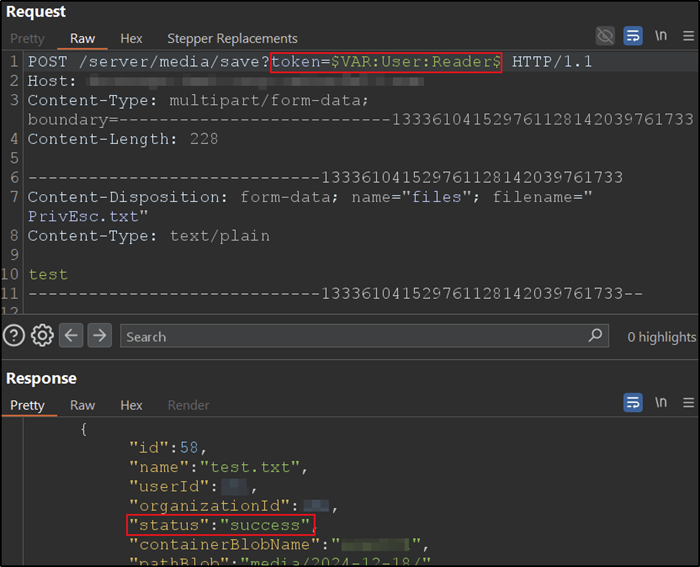
Example of a call to delete media from another user:
Deleting saved locations (horizontal privilege escalation)
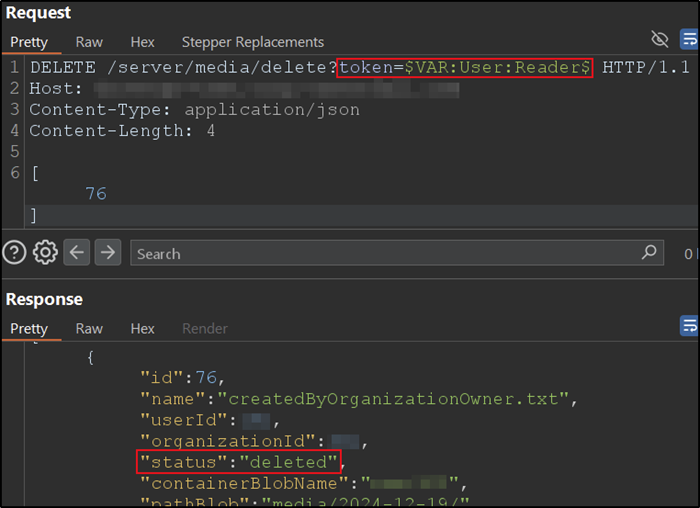
The application allows users to delete saved locations of other users. The following screenshot shows how a user saves a location:
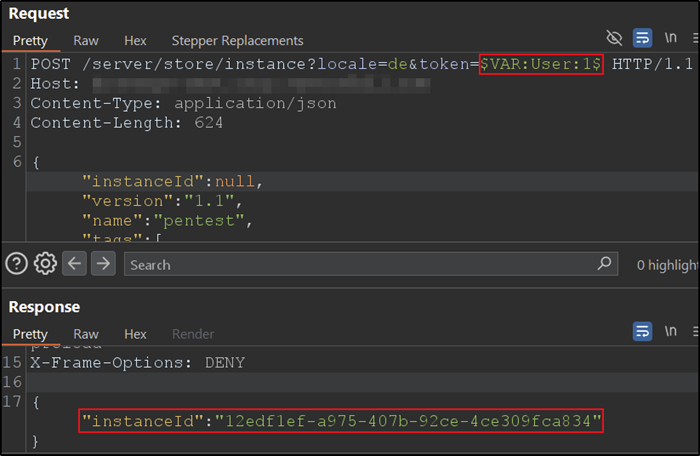
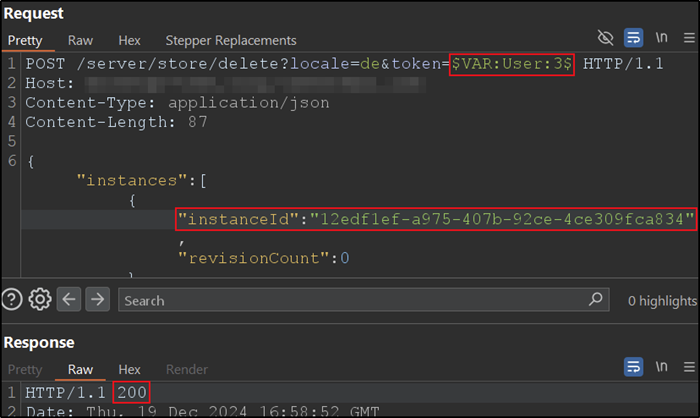
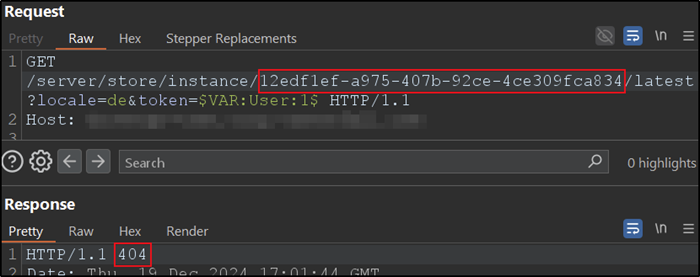
The location with the ‘instanceId’ shown in the screenshot above can then be deleted by another user:
As can be seen in the following screenshot, the location was actually deleted:
Affected components: File upload, saved locations
Attack type: Remote
Impact: Privilege escalation
Attack vectors: To exploit the vulnerability, an attacker must have access to the application, i.e. a user account. Depending on the configuration, this can be created by themselves.
Reference: https://www.droneharmony.com/post/security
Discoverer: André Eikmeier (mgm security partners)
Arbitrary file type upload allowed
Description
The application offers various file upload options that should only allow certain file types. However, some of these upload functions do not check the file type. During the test, it was possible to upload a .com file to the server (shown here using the example of uploading media/images):
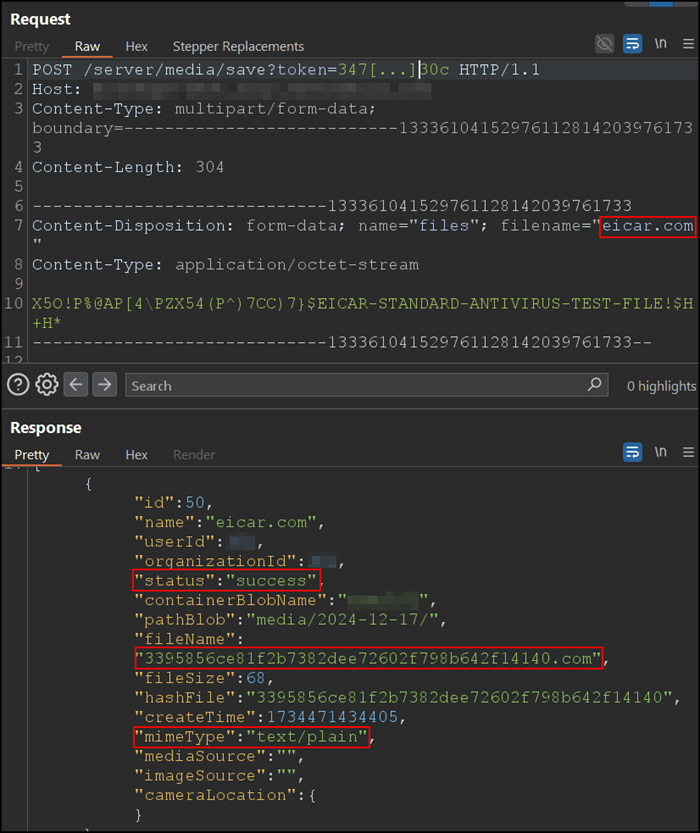
This file could then be downloaded again:
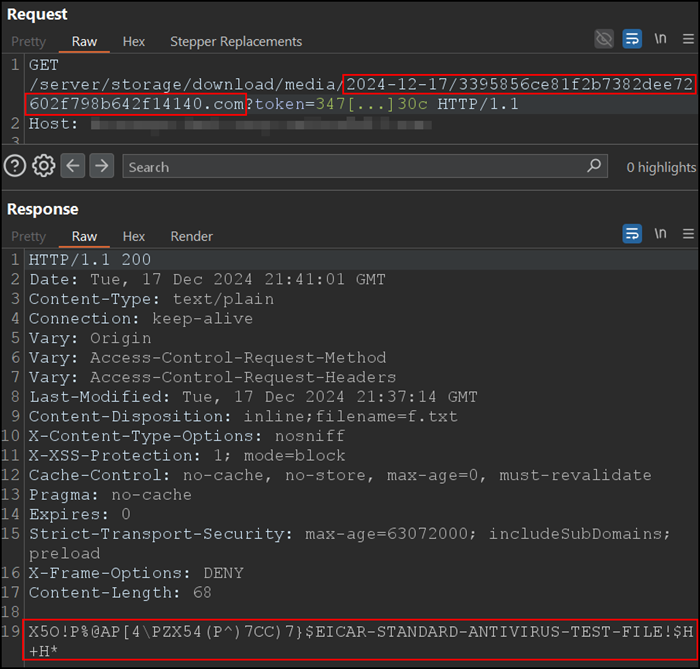
This allows attackers to upload potentially harmful files such as viruses or HTML files containing malicious JavaScript.
Affected components: File upload
Attack type: Remote
Attack vectors: To exploit the vulnerability, an attacker must have access to the application, i.e., a user account. In some circumstances, this can be created independently.
Reference: https://www.droneharmony.com/post/security
Discovered by: André Eikmeier (mgm security partners)
Reflected cross-site scripting
Description
As described above, the application allows the upload of arbitrary files. This includes uploading HTML files with malicious JavaScript:
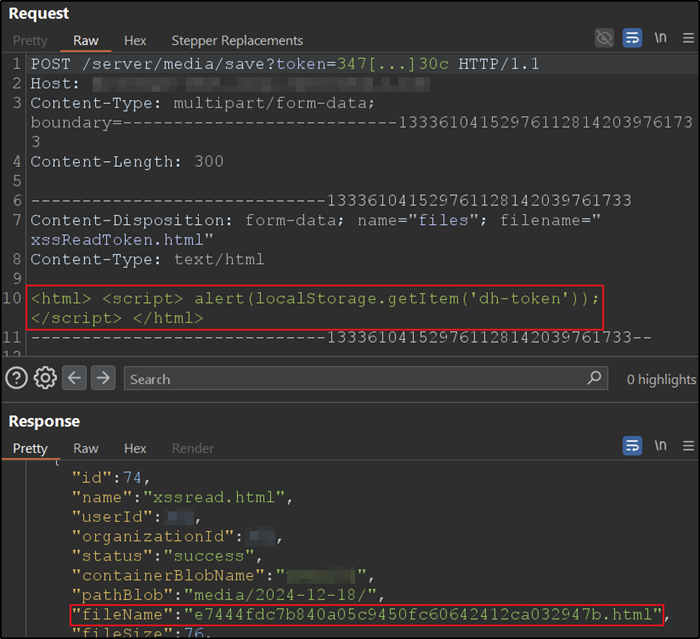
Nun kann der Angreifer einem beliebigen anderen Nutzer einen Download-Link für diese schädliche HTML-Datei senden, in diesem Fall: https://{host}/server/storage/download/media/{date}/{fileName}?token={attacker_session_token}. Wenn der angegriffene Nutzer auf den Link klickt, wird die HTML-Datei geöffnet und das schädliche JavaScript ausgeführt. So könnte ein Angreifer beispielsweise auf den Session-Token des Opfers zugreifen, wenn dieses sich vorher angemeldet hat und bei der Anmeldung die Option „Angemeldet bleiben“ ausgewählt hat:
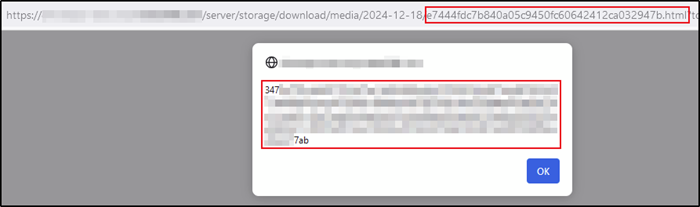
Remark: It should be noted that the session token in the malicious link is the session token of the attacker, which authorizes the victim to download the file uploaded by the attacker. However, the session token that the JavaScript accesses is actually the session token of the victim. This vulnerability exploits both the vulnerability of uploading arbitrary file types described above and the vulnerability of the session token transmitted in the URL described below.
Affected components: File upload
Attack type: Remote
Impact: Disclosure of sensitive information
Attack vectors: To exploit the vulnerability, an attacker must have access to the application, i.e., a user account. In some circumstances, this can be created independently.
Reference: https://www.droneharmony.com/post/security
Discovered by: André Eikmeier (mgm security partners)
Transmission of the session token in the URL
Description
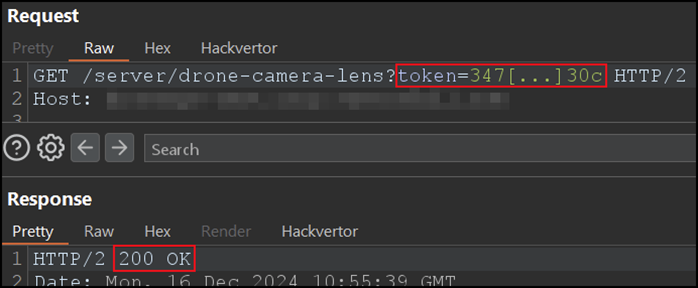
The session token enables access to a user's session. However, the token is transported in the URL and is therefore unnecessarily exposed. If an attacker has access to logs or caches such as server logs or the browser cache, they can read the token and gain access to the corresponding user account if the token is still active.
In addition, the session token can potentially be disclosed when sharing links carelessly with third parties.
The following screenshot shows an example HTTP request to the backend, which is made by the application with the token in the URL:
Affected components: Session management
Attack type: Remote
Impact: Disclosure of sensitive information
Attack vectors: To exploit the vulnerability, an attacker must have access to the browser's or reverse proxy's cache, or act as a man-in-the-middle to read the URLs.
Reference: https://www.droneharmony.com/post/security
Discovered by: André Eikmeier (mgm security partners)
MQTT password visible in the web application
Description
The dashboard of the web application displays an overview of the parameters for setting up the drone dock, including the password for the user's MQTT account:
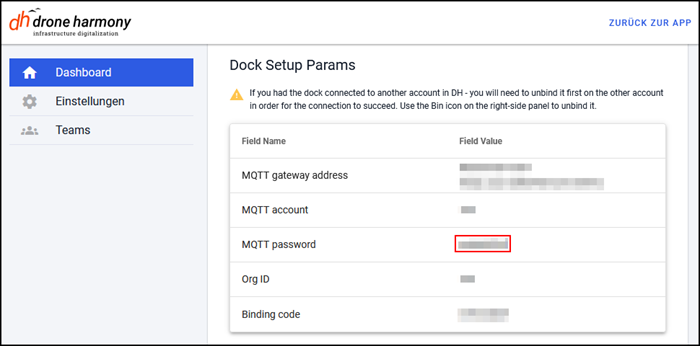
This allows an attacker to read the password, for example via cross-site scripting, and gain access to the MQTT account and thus to the user's entire communication with the drone.
Affected components: Dashboard
Attack type: Remote
Impact: Disclosure of sensitive information
Attack vectors: To exploit the vulnerability, an attacker must have access to the corresponding user account or exploit a cross-site scripting vulnerability, for example.
Reference: https://www.droneharmony.com/post/security
Discovered by: André Eikmeier (mgm security partners)

